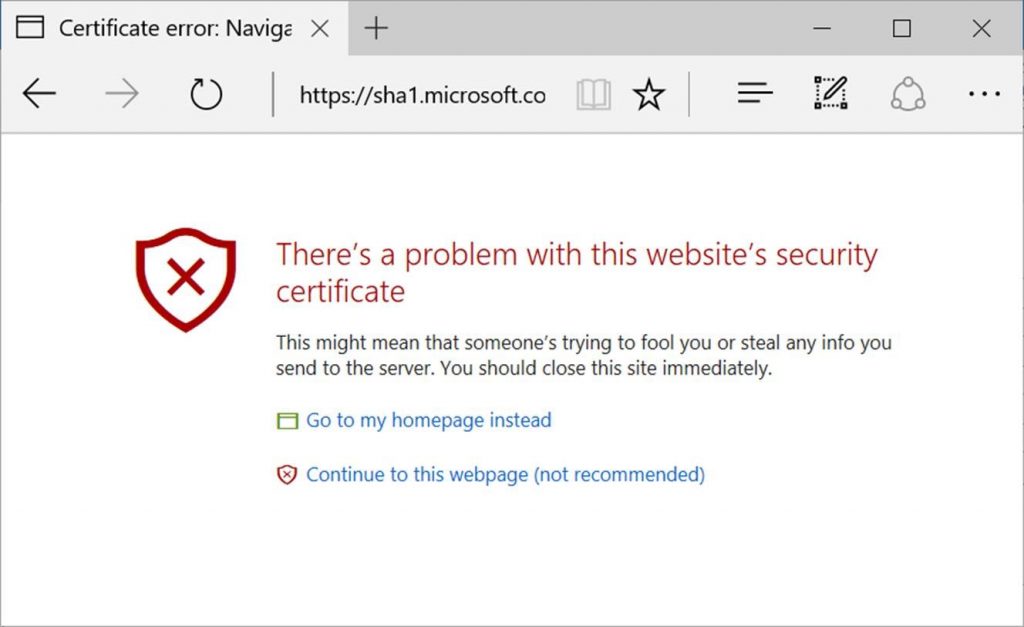
Update (4/26/2017): Starting on May 9, 2017, Microsoft Edge and Internet Explorer 11 will prevent sites that are protected with a SHA-1 certificate from loading and will display an invalid certificate warning. Additionally, the Windows 10 Creators Update blocks SHA-1 by-default in the browser. Customers who would like to disable SHA-1 today may do so with the instructions below.
This will only impact SHA-1 certificates that chain to a Microsoft Trusted Root CA. Manually-installed enterprise or self-signed SHA-1 certificates will not be impacted, although we recommend for all customers to quickly migrate to SHA-256.
Additional information on Microsoft’s overall SHA-1 deprecation plans can be found on TechNet.
Frequently asked questions
How can I disable SHA-1 today?
You can disable SHA-1 today test by running the following commands from an Administrator Command Prompt:
First, create a logging directory and grant universal access:
[code language=”powershell”]
set LogDir=C:Log
mkdir %LogDir%
icacls %LogDir% /grant *S-1-15-2-1:(OI)(CI)(F)
icacls %LogDir% /grant *S-1-1-0:(OI)(CI)(F)
icacls %LogDir% /grant *S-1-5-12:(OI)(CI)(F)
icacls %LogDir% /setintegritylevel L
[/code]
Next, enable certificate logging and SHA-1 blocking:
[code language=”powershell”]
Certutil -setreg chainWeakSignatureLogDir %LogDir%
Certutil -setreg chainWeakSha1ThirdPartyFlags 0x80040004
[/code]
Important: Use the following commands to remove the settings after you have completed your testing.
[code language=”powershell”]
Certutil -delreg chainWeakSha1ThirdPartyFlags
Certutil -delreg chainWeakSignatureLogDir
[/code]
How will other Windows applications and older versions of Internet Explorer be impacted?
Third party Windows applications that use the Windows cryptographic API set and older versions of Internet Explorer will not be impacted by the mid-2017 changes by-default.
How will SHA-1 client authentication certificates be impacted?
The mid-2017 update will not prevent a client using a SHA-1 signed certificate from being used in client authentication.
What about cross-signed certificates?
Windows will only check if the thumbprint of the root certificate is in the Microsoft Trusted Root Certificate Program. A certificate cross-signed with a Microsoft Trusted Root that chains to an enterprise/self-signed root would not be impacted by the changes planned for mid-2017.
― Alec Oot, Senior Program Manager
― Jody Cloutier, Senior Program Manager
