Trusted Cyber Physical Systems looks to protect your critical infrastructure from modern threats in the world of IoT
This week at Hannover Messe 2018 in Germany, we are excited to demonstrate how Microsoft is utilizing its more than 25 years of embedded and hardware security experience with a new project codenamed Trusted Cyber Physical Systems (TCPS).
As the Internet of Things gains momentum with millions of devices connected to one another, it has become more challenging to secure these devices and services given their increasing complexity. Over the last few months, we have already witnessed attacks to critical infrastructure around the world from Triton infiltrating the control and safety systems of an oil and gas plant to NotPetya shutting down production at a pharmaceutical factory. We can no longer ‘simply’ connect our devices without building in end-to-end security because the financial toll is not the only risk but the risk to human lives and property is too great.
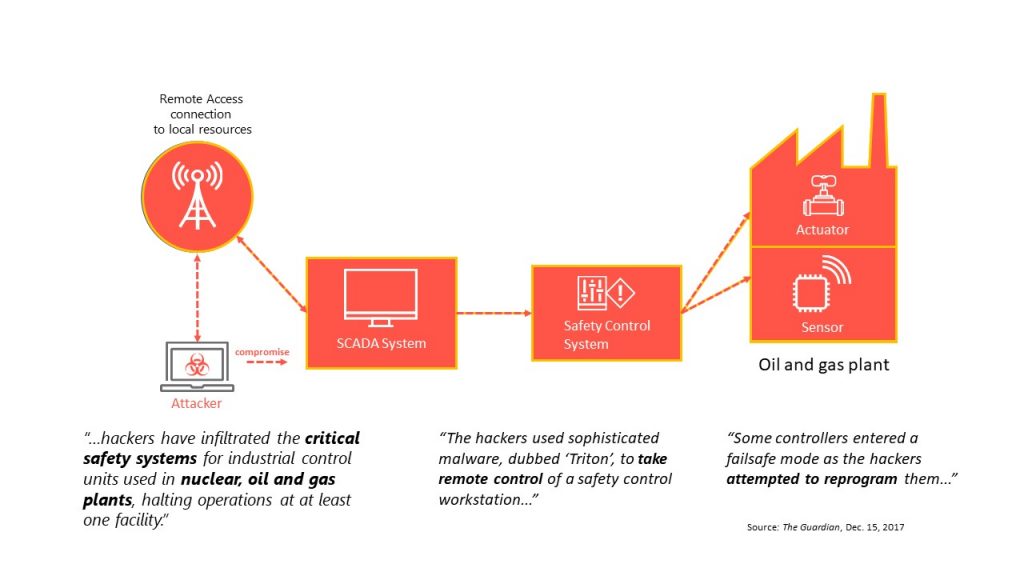
The Triton attack on the control and safety systems of an industrial plant brought to the forefront system vulnerabilities in critical infrastructure even when they are designed with failsafe controls. Attackers used sophisticated malware to remotely control a safety control workstation. Some controllers accidently triggered failsafe mode as the attackers tried to reprogram them. This attack brought to light two challenges prevalent in today’s connected world – a need to prevent malware from taking control of key operations and a hackers’ ability to leverage third-party operators such as admins of cloud hosting services, or OS, and driver vendors to introduce malware.
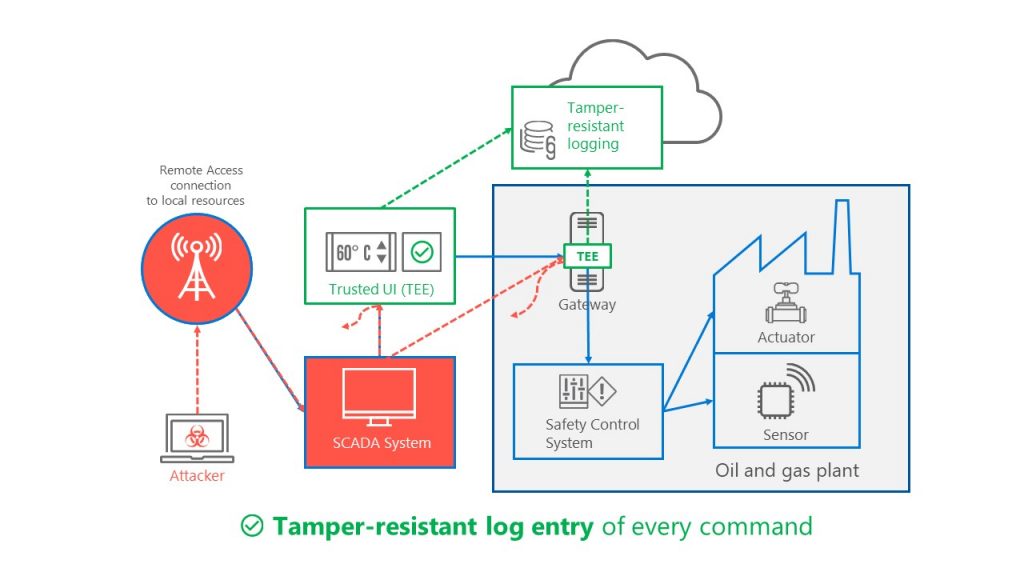
Microsoft’s Trusted Cyber Physical Systems (TCPS) efforts address these challenges to secure critical infrastructure by creating a security pattern to process critical data throughout distributed systems. Data in execution must be protected by Trusted Execution Environments (TEEs) such as Intel SGX, ARM TrustZone, and SecureElements. Components must not only use secure protocols, and protect keys and data at rest, they must also perform all critical operations in a TEE that is protected from public cloud hosters and OS vendors. Our overarching security principle for TCPS is that the solution owner/operator must not lose control over their critical systems.
Here is how Trusted Cyber Physical Systems is realized with the following four properties:
- Separation of critical execution: Help protect critical infrastructure from malware threats by separating non-critical from critical operations and concentrating on using hardware isolation to protect control of physical systems.
- Inspectability of execution process: Ensure that any code that handles critical operations must be auditable by operators through source code review.
- Attestability of processing environment: During operation, each component must be able to verify that data is received and sent only from trustworthy sources. A component also needs to attest its trustworthiness to other components.
- Minimizing number of entities that need to be trusted: Reducing the number of trusted entities significantly reduces the attack surface for critical infrastructure. In the ideal TCPS solution, the operator will maintain the only root of trust for critical code execution.
Why work with Microsoft on securing your Critical Infrastructure?
- We at Microsoft have taken a holistic approach with TCPS based on years of security, cloud, and embedded experience.
- With TCPS, you can be assured that code inspection by customers and third parties will be on Microsoft-provided trusted applications and services.
- Azure confidential computing brings trusted execution to the cloud
- The Windows IoT Device Update Center can be used to deliver patches via the Windows Update global CDN
- Windows 10 IoT Core support for NXP i.MX 6 and i.MX 7 enables TCPS to the wire with trusted I/O
- Leaders in cross-platform industry standards efforts (ex: OPC, IIC, TCG, IETF)
Microsoft and our partners are seeking to unlock trusted execution in the cloud, on devices controlling infrastructure and on edge devices. The power of TCPS brings trusted execution to the wires and pins that control critical infrastructure, enabling end-to-end critical infrastructure solutions.
You can find-out more about what we’re building and how to partner with us in bringing these solutions to market. If you are attending Hannover Messe Industry 2018, please visit us at Hall 7 C40. You can also learn more via our Whitepaper, overview of TCPS or contact us at [email protected].
