Today we are pleased to release a new Insider Preview build of the Windows Server VNext Semi-Annual Channel release, and Windows Admin Center Preview 1812.
PLEASE NOTE: In-place upgrade will fail for this build – a clean install is required.
What’s New in Windows Server
WDAC – Composable (stacked) code integrity policies for supporting multiple code integrity policies
WDAC brings you the ability to support multiple CI policies. Three scenarios are now supported:
- Scenario 1 – Deploy a “base” policy in enforcement mode and deploy a second “audit” policy side-by-side to support validation of policy changes before deploying in enforcement mode. (Intersection)
- Scenario 2 – Enforce 2 or more “base” policies simultaneously to allow simpler policy targeting for policies with different scope/intent, e.g., Base1 corporate standard policy that is relatively loose to accommodate all organizations while forcing minimum corp standards (e.g. Windows works + Managed Installer + path rules). Base2 team specific policy that further restricts what is allowed to run (e.g. Windows works + Managed Installer + corporate signed apps only) (Intersection)
- Scenario 3 – Supplemental policies deployed to expand Base policy, e.g., Azure host baseline policy restricts tightly to just allow Windows and hardware drivers allows supplemental policies. Exchange Azure team supplemental policy adds just the additional signer rules needed to support Exchange team signed code. (Union)
What’s New in Windows Admin Center
Thank you for your continued interest in Windows Admin Center! Following the update to our generally available channel earlier this month, the Windows Admin Center Preview resumes with this 1812 release. This is the first release where you’ll be able to preview the dark UI theme, which is still a work in progress.
Other new features are:
- Power configuration tab on the server settings page, where you can change the configured power profile.
- If the server has an IPMI-compatible BMC, you’ll find the BMC serial number and a hyperlink to its IP address on the Server Overview page.
- If Windows Admin Center is installed in service mode, you can now use PowerShell to automate the following (examples included below):
- Import/export of connections (with tags)
- Extension management
We have also improved the High-Availability deployment experience and script. View the new documentation here.
Dark Theme (preview)
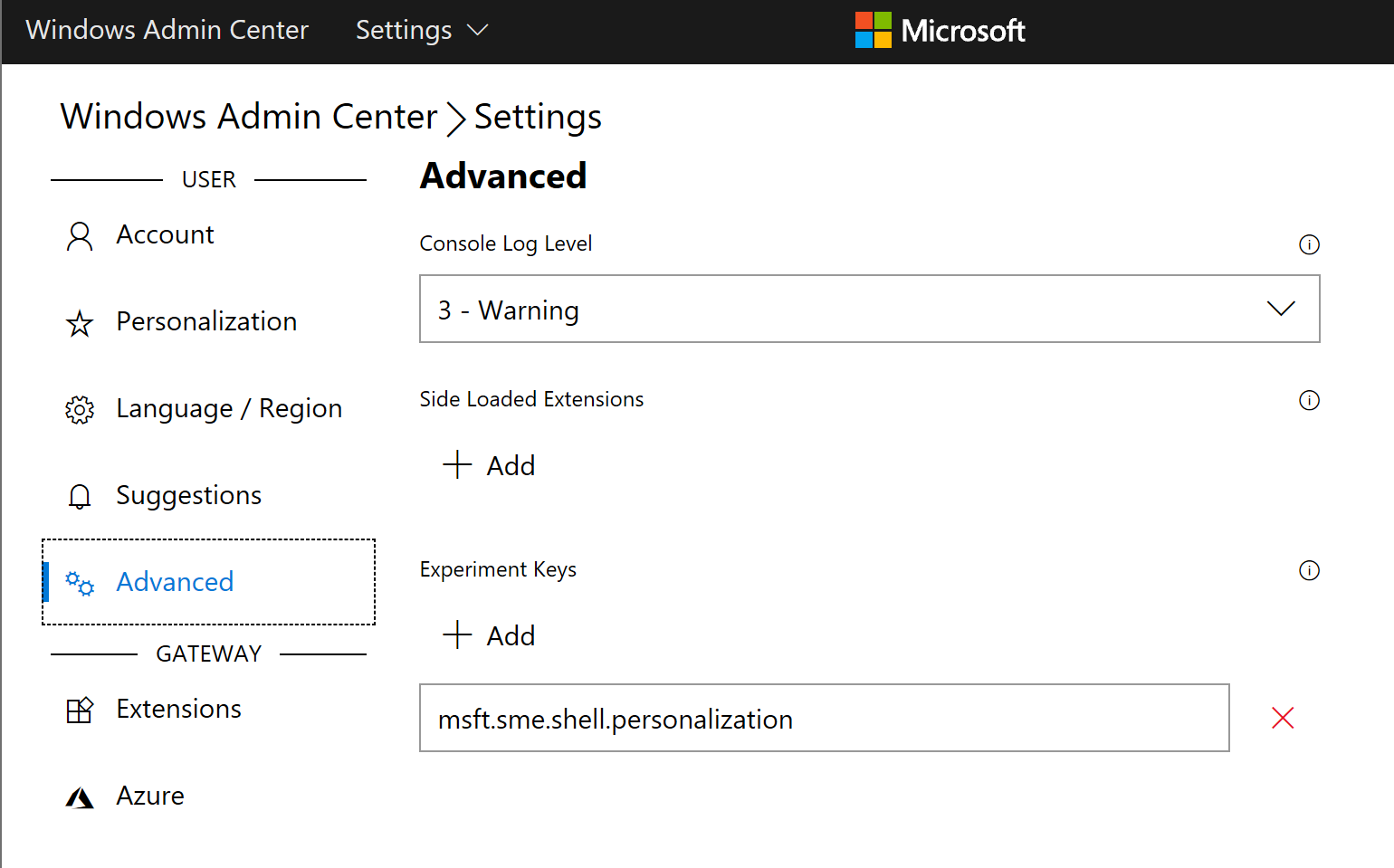
To enable the dark theme, enter the experiment key msft.sme.shell.personalization on the advanced tab of the global settings. This will enable a new personalization tab, where you can toggle to the dark theme.
NOTE: Dark theme is still a work in progress, please do not report bugs at this time.
Configure Windows Admin Center using PowerShell
After installing this release, you’ll find two new PowerShell modules that you can use to automate Windows Admin Center configuration when it is installed as a server service.
NOTE: Windows Admin Center installed in desktop mode is not supported.
Extension management
[code language=”powershell”]
# Add the module to the current session
Import-Module "$env:ProgramFiles\windows admin center\PowerShell\Modules\ExtensionTools"
# Available cmdlets: Get-Feed, Add-Feed, Remove-Feed, Get-Extension, Install-Extension, Uninstall-Extension, Update-Extension
# List feeds
Get-Feed "https://wac.contoso.com"
# Add a new extension feed
Add-Feed -GatewayEndpoint "https://wac.contoso.com" -Feed "\\WAC\our-private-extensions"
# Remove an extension feed
Remove-Feed -GatewayEndpoint "https://wac.contoso.com" -Feed "\\WAC\our-private-extensions"
# List all extensions
Get-Extension "https://wac.contoso.com"
# Install an extension (locate the latest version from all feeds and install it)
Install-Extension -GatewayEndpoint "https://wac.contoso.com" "msft.sme.containers"
# Install an extension (latest version from a specific feed, if the feed is not present, it will be added)
Install-Extension -GatewayEndpoint "https://wac.contoso.com" "msft.sme.containers" -Feed "https://aka.ms/sme-extension-feed"
# Install an extension (install a specific version)
Install-Extension "https://wac.contoso.com" "msft.sme.certificate-manager" "0.133.0"
# Uninstall-Extension
Uninstall-Extension "https://wac.contoso.com" "msft.sme.containers"
# Update-Extension
Update-Extension "https://wac.contoso.com" "msft.sme.containers"
[/code]
Export/import of connections
[code language=”powershell”]
# Add the module to the current session
Import-Module "$env:ProgramFiles\windows admin center\PowerShell\Modules\ConnectionTools"
# Available cmdlets: Export-Connection, Import-Connection
# Export connections (including tags) to .csv files
Export-Connection "https://wac.contoso.com" -fileName "WAC-connections.csv"
# Import connections (including tags) from .csv files
Import-Connection "https://wac.contoso.com" -fileName "WAC-connections.csv"
[/code]
Windows Admin Center Known Issues
Extension Manager
If you have upgraded from an older version, extension manager will display an old version number for pre-installed extensions, however the actual tool UI will be up to date. This will block you from removing pre-installed extensions. Extensions from feeds will continue working normally.
To resolve this issue, close Windows Admin Center, delete the ‘%ProgramData%\Server Management Experience\Extensions’ directory, and restart Windows Admin Center.
Available Content
- Windows Server vNext Semi-Annual Preview The Server Core Edition is available in the 18 supported Server languages in ISO format and in English only in VHDX format.
- Windows Server Core App Compatibility FoD Preview
- Windows Server Language Packs
- Windows Admin Center 1812
The following keys allow for unlimited activations of Windows Server Previews:
- Server Standard: V6N4W-86M3X-J77X3-JF6XW-D9PRV
- Server Datacenter: B69WH-PRNHK-BXVK3-P9XF7-XD84W
This Windows Server Preview will expire July 5th, 2019.
Symbols are available on the public symbol server – see Update on Microsoft’s Symbol Server blog post and Using the Microsoft Symbol Server. Matching Windows Server container images will be available via Docker Hub. For more information about Windows Server containers and Insider builds, click here.
How to Download
Registered Insiders may navigate directly to the Windows Server Insider Preview download page. If you have not yet registered as an Insider, see GETTING STARTED WITH SERVER on the Windows Insiders for Business portal.
We value your feedback!
The most important part of a frequent release cycle is to hear what’s working and what needs to be improved, so your feedback is extremely valued. For Windows Admin Center, Send us feedback via UserVoice. We also encourage you to visit the Windows Admin Center space on the Microsoft Tech Communities forum to collaborate, share and learn from experts.
For Windows Server, use your registered Windows 10 Insider device and use the Feedback Hub application. In the app, choose the Windows Server category and then the appropriate subcategory for your feedback. In the title of the Feedback, please indicate the build number you are providing feedback on in this format:
[Server #####] Title of my feedback
We also encourage you to visit the Windows Server Insiders space on the Microsoft Tech Communities forum to collaborate, share and learn from experts.
Windows Server Bug Fixes
- We fixed an issue where a password change could result in the next unlock hanging for domain joined AD users.
- We fixed an issue addressing frequent access violations in bindflt!BfNormalizeNameComponentExCallback.
- We fixed an issue where SRV2.sys may crash with an access violation when attempting to connect to a client machine with a null name string.
- We fixed an issue where OpenId Connect sign-on applications may experience high latency in ADFS authentication when using SAML and Oauth code flow.
- We fixed an issue where an occasional corruption may occur in UserName information on events retrieved using PowerShell cmdlet Get-RemoteAccessConnectionStatistics.
- We fixed an issue where using classic file explorer in Server core from the App Compat FOD, clicking Eject on a USB device would notify the user that the USB Drive is currently in use, resulting in a hung eject operation.
- We fixed an issue where virtual machine runtime state (VMRS) files failed to load. An affected system may report a failure in looking up or receiving the VM from the source host due to the data being invalid (0x8007000d).
Windows Server Known Issues
- [New] Dynamic Update Setup on Server shows “Installing Windows 10” instead of Server.
- [New] Scheduled startup tasks may fail to run. An event is logged, ID 101 with the error code ERROR_LOGON_FAILURE when the failure occurs.
- [New] A virtual machine may not report all virtual fibre channel (vfc) LUNs after powering on if there are 2000+ vfc LUNs. WMI queries from the host show the LUNS available. Restarting the VMMs may show the LUNS again as available.
- [New] DCPromo fails if the interface metric of the physical NIC is larger than Loopback Interface
- [New] ADFS Requests with invalid domain suffixes fail after a long delay (around 3 minutes) with error DS_NAME_ERROR_DOMAIN_ONLY. This can cause queued legitimate requests to experience delays or also timeout.
- Server FODs are not retained after in-place (or B2B) upgrade
- [New] Domain Controller rename updates incorrect attributes in AD leaving orphaned data behind (ValidateSPNsAndDNSHostNameActual). This can be reproduced by adding a new FQDN, setting it as primary, restarting the domain controller, then removing the current FQDN. Checking the msDS-AdditionalDnsHostName, msDS-AdditionalSamAccountName and servicePrincipalName attributes will incorrect values.
- [New] Invalid file may be created in %Systemroot%\System32\LogFiles\Sum by User Access Logging
- [New] Windows may attempt to reuse an expired DHCP lease if the lease expired while the OS was shutdown.
- Self-service users cannot install Feature on Demand (FOD) packages and Language Packs for Windows Server Update Service (WSUS), System Center Configuration Manager (SCCM), and Autopilot scenarios.
A container host may become unresponsive due to a deadlock when attempting to mount a volume. On an affected system, Docker hangs on all commands. - The operating system has an unnecessary utility account for Windows Defender Application Guard.
When a Windows Defender Application Guard container crashes, the resulting type of dump may be unexpected. - [New] CPU spike may happen when Windows Server logs obsolete Windows Error Reporting reports PnPDriverInstallError and PnPDriverImportError.
Terms of Use
This is pre-release software – it is provided for use “as-is” and is not supported in production environments. Users are responsible for installing any updates made available from Windows Update. All pre-release software made available to you via the Windows Server Insider program are governed by the Insider Terms of Use.
No downtime for Hustle-As-A-Service,
Dona <3